Along with all of the auto festivities this week in Dallas, it’s also Data Privacy Week, which is orchestrated by the National Cybersecurity Alliance (NCA).
After expanding Data Privacy Day into a week-long initiative for the first time last year, NCA highlighted Data Privacy Week will continue to raise awareness about the importance of digital privacy for consumers and businesses.
The campaign’s themes focus on reinforcing consumer knowledge about personal data protection while addressing business’ responsibility for ethical user privacy and data collection practices.
“Data Privacy Week is critical for arming consumers with the tools they need to take ownership of their digital identities and to remind them to think critically about who they share their data with and how to protect it,” NCA executive director Lisa Plaggemeier said in a news release.
“It’s also a platform to emphasize why businesses must maintain a gold standard of respect and transparency around how they collect, store and use consumer data, alongside the benefits of doing so,” Plaggemeier continued.
This year's Data Privacy Week is sponsored by Microsoft (platinum sponsor) and Optiv (silver sponsor) and focuses on content centered around the following themes:
• Data: The Story of You – All your online activity generates a trail of data. Websites, apps, and services collect data on your behaviors, interests, and purchases. Sometimes, this includes personal data, like your Social Security and driver’s license numbers. It can even include data about your physical self, like health data – think about how a smartwatch counts and records how many steps you take. While it’s true that you cannot control how each byte of data about you and your family is shared and processed, you are not helpless. In many cases, you can control how you share your data with a few simple steps. Remember, your data is precious, and you deserve to be selective about who you share it with!
• For Organizations: Respect Privacy: Respecting the privacy of your customers, staff, and all other stakeholders is critical for inspiring trust and enhancing reputation. According to the Pew Research Center, 79% of U.S. adults report being concerned about the way their data is being used by companies. By being open about how you use data and respecting privacy, you can stand out from your competition.
In addition to a collection of educational materials available for public consumption, NCA is hosting a series of events featuring privacy experts, policymakers and engineers to promote the campaign’s core themes. These include:
• Data: The Story of You – On Tuesday at noon (ET), experts will discuss best practices around protecting data trails associated with individual users and their families.
• Data Privacy Week #PrivacyChat – On Wednesday at 2 p.m. (ET), users can tune into NCA’s (@StaySafeOnline) Twitter chat to share top tips, advice and resources for consumers and businesses, as well as connect with other data privacy and security advocates and educators. More information about this event can be found here
• Designing a Privacy-First World – On Thursday at 2 p.m. (ET), experts will convene to discuss why data privacy is becoming a more central issue with each passing year, as well as why the concept must be a key design component for any product, business or society with data privacy in mind. More information about this event can be found here.
“Microsoft is delighted to be the lead sponsor of Data Privacy Week 2023, a pivotal year for privacy around the globe,” said Julie Brill, chief privacy officer and corporate vice president at Microsoft.
“To realize the profound benefits of technology we believe organizations and governments need to use data responsibly and recognize privacy as a fundamental human right. With rapidly advancing technology, protecting privacy has never been more important for the long-term success of any organization, including Microsoft,” Brill went on to say.
Data Privacy Week builds on the success of Data Privacy Day which began in the United States and Canada in January 2008 as an extension of Data Protection Day in Europe. Data Protection Day commemorates the Jan, 28, 1981 signing of Convention 108, the first legally binding international treaty dealing with privacy and data protection.
To become a Data Privacy Week Champion, visit https://staysafeonline.org/programs/data-privacy-week/champion.
For more information about NCA’s Data Privacy Week, visit https://staysafeonline.org/programs/data-privacy-week.
Ahead of Martin Luther King Day, Mendoza Ventures said it has closed its third fund.
The female- and Latinx-founded fintech, artificial intelligence and cybersecurity venture capital firm landed a $100 million fund that Mendoza Ventures said it will invest in early growth stage startups with a focus on diverse teams.
The initial close was led by Bank of America, and included Grasshopper Bank and other investors.
“As a female- and Latinx-founded and -led venture fund, we are uniquely positioned to fund the series A to B for diverse or female led founders,” Mendoza Ventures general partner Adrian Mendoza said in a news release. “This is one of the very few diverse-led VC funds that are funding at this stage especially in a market where capital is shrinking for diverse founders.”
Mendoza Ventures explained Fund II’s capital allocation of 80% to underrepresented founders — defined as female, immigrant, person of color or LBGTQ — underscores how these commitments have ripple effects from diverse founders to impacting diverse communities through fintech.
The firm added Fund III breaks the $100 million “glass ceiling” for female and diverse GPs in Venture Capital and fill in the early growth capital gap for diverse and female-led startups.
“Bank of America’s investment into Mendoza Ventures underscores our ongoing efforts to address the persistent gap in access to growth capital for minority- and women-led businesses,” said Renee Nalbandyan, director in global corporate strategy at Bank of America.
“Mendoza Ventures is at the forefront of supporting innovation and driving diversity not only within venture capital, but also across the fintech industry, and our investment is a step towards creating positive change and more economic opportunities across the country.”
The news release also mentioned the anchor funding comes from Bank of America as part of its commitment to advancing racial equality and economic opportunity, of which more than $400 million is allocated to investments in mission-focused venture funds.
As automobiles have become more technically connected to the world, the news is filled with apocryphal warnings about virtual carjackers — or maybe car-hackers is a better term. While there are also real issues with new vehicles and cyber security, no automotive business would dream of leaving the keys on the counter, digital or otherwise.
But cyber threats can come from a more mundane source: the back office. Many companies haven’t thought to safeguard their printers from attack by malicious actors. Because printers are a conduit for highly sensitive information, businesses can and should take as much care protecting these devices from data breaches and cybersecurity attacks as they do to prevent auto theft.
From finance applications and sales orders to commission reports and service orders, printed documents remain the backbone of the automotive industry, despite the push for digital transformation. At the same time, this reliance on printed documents leaves businesses vulnerable to a host of security incidents. In fact, over two-thirds of businesses experienced some form of data loss in the last 12 months due to unsecure printing practices.
While some of these incidents — like the recent data breach experienced by Oscar Health Plan of California — can be attributed to printer errors, others represent sophisticated attacks by malicious actors seeking access to information they can sell on the dark web. In a recent high-profile case, criminals disabled printers that confirmed SWIFT network transfers during attacks on numerous banks in India. Another serious incident involved ransomware known as Mamba, or HDDCryptor, that shut down printers by blocking server messages, enabling the ransomware to spread across network shares.
Regardless of their cause, data breaches can carry a high price in terms of litigation, reputational damage and regulatory fines. In one case, the Department of Health and Human Services fined a company $1.2 million for HIPAA violations because they failed to erase Protected Health Information (PHI) stored on a leased printer. Moreover, because modern printers are integrated with business networks through Wi-Fi connections and ethernet and form an integral part of the Internet of Things, they are more susceptible to serious security incidents than first-generation printers, which connected to standalone mainframes through various physical peripheral interfaces.
Although manufacturers are aware of the security vulnerabilities associated with modern printers, the businesses that use their products don’t always take the necessary precautions to safeguard these devices. In one survey, fewer than half of IT professionals deployed any form of printer protection. Moreover, they ranked printer security below that of cloud and hybrid platforms and traditional endpoints, despite the security risks associated with printing devices.
While printers haven’t received the same level of attention as traditional endpoints, businesses have a lot of options when it comes to protecting these devices. A good place to start is government publications like NIST 800-53, which outlines security and privacy controls for information systems, and the IRS 1075 Revised Publication, which includes guidelines for protecting Federal Tax Information. The Security Technical Implementation Guides (STIGs) developed by the US Defense Information Systems Agency are excellent resources that provide device hardening standards used by the IRS and other federal agencies.
Whatever guidance you employ, you should treat your printers with the same care you take with other network devices. At a minimum, you should include your printers in quarterly vulnerability scans. You should also configure your printers to record all relevant system activity and send alerts of any significant events like audit processing failures. For example, you can configure printers to recognize user-defined terms or text strings that tag output as confidential. When a match is detected, the printer will send an alert containing job details and content to the system administrator.
Employing pull printing and robust authentication methods are other effective safeguards. With pull printing, a user must provide authentication using smart cards, biometrics, and other methods before they can collect printed documents. You’ll also want to close any unused or unnecessary printer ports and ensure your printer vendor uses a Center for Internet Security (CIS) benchmark for the printer’s operating system. As one example, Xerox requires all printers to adhere to federal hardening standards outlined in a benchmark called the Federal Overlay.
Another option for securing your printers is to outsource your jobs to a secure managed print services provider (MPS). As the data breach with Oscar Health Plan indicates, you will want to conduct thorough due diligence to ensure you select a secure vendor if you decide to outsource. In addition to verifying the vendor employs appropriate technical safeguards like encryption, intrusion prevention and endpoint detection and response, check whether they conform to data protection standards outlined in an industry-recognized security framework like NIST’s Cybersecurity Framework. You should also verify that the vendor undergoes some form of periodic assessment by an independent third party, either as part of a security certification like HITRUST or ISO 27001 or the AICPA’s SOC 1 and SOC 2 reporting.
Because of the sensitivity involved in transactional documents, such as credit applications, businesses in the automotive industry must take appropriate measures to protect their printers from malicious attacks and other vulnerabilities. Like the disabling features and anti-theft devices we install on our cars, printer security measures can prevent valuable assets from loss. With a little care, you can protect sensitive printed information and keep your business from becoming the next headline associated with a serious data breach or security incident.
Steve Berman is director of risk and compliance for DATAMATX, one of the nation’s largest privately held full-service providers of high-volume print and electronic transactional communications. For more information, visit www.datamatx.com.
Inovatec Systems now has some proof about its platform security.
The provider of cloud-based software solutions for finance companies and other lenders announced on Tuesday that that its platform has obtained ISO 27001 certification of its information management system, ensuring that all data privacy and information security activities comply with strict ISO 27001 mandates.
The certification was conducted by Schellman Compliance, an ANAB and UKAS accredited certification body based in the United States.
Inovatec explained ISO 27001 is a globally recognized standard for the establishment and certification of an information security management system (ISMS). The standard specifies the requirements for establishing, implementing, operating, monitoring, reviewing, maintaining and improving a documented ISMS within the context of the organization’s overall business risks. It sets forth a risk-based approach that focuses on adequate and proportionate security controls that protect information assets and give confidence to interested parties.
“Achieving ISO 27001 certification involves a rigorous methodology that includes the thorough testing and validation of all the technologies and workflows associated with the management, transport, and storage of sensitive personal information and financial data,” Inovatec chief operating officer Danijela Kovacevic said in a news release. “Our clients can be confident that Inovatec’s information security practices are well-suited to satisfying their sophisticated needs.”
Inovatec’s cloud-based technology can enable finance companies and other lenders to streamline processing, decisioning and management with intelligent automation that can be configured to meet users’ needs.
The company’s systems can allow clients to adjust workflows as needed, helping them to grow their business in a competitive industry, without compromising on data security, privacy, and regulatory compliance.
For information on Inovatec’s integrated loan origination system, loan management system, and customer portal solution, visit www.inovatec.com.
A cybersecurity company known for “ethical hacking” and advising Fortune 500 firms as well as federal, state and local governments is about to move into a new headquarters.
TrustedSec is hosting a grand opening ceremony on May 6 for its new corporate complex in Fairlawn, Ohio. The new facility contains 20,000 square feet and includes state-of-the-art cybersecurity features, including a cyber war room, digital forensics lab, cyber incident intrusion center and a device hacking lab for testing Internet of Things (IoT) devices.
The company highlighted its new complex also serves as a cybersecurity hub both regionally and globally, including a cutting-edge “hacking bay” where the company will host advanced security training, hacking workshops and coding events for the information security community, businesses and students.
“We are excited to begin TrustedSec’s next chapter in Fairlawn, where we have big plans not only for the company, but also for the local community,” said David Kennedy, the founder and chief executive officer of TrustedSec and a former hacker for the National Security Agency.
“Cybersecurity has never been more important than it is right now, between the rise in geopolitical tensions and the continuing surge in ransomware and financial fraud attacks,” Kennedy continued in a news release. “Companies are on the front lines of this new cyber conflict, and we are seeing a tremendous increase in demand for our services.
“With our new complex in Fairlawn, we will be able to not only expand our business operations, but also position the region as a central hub for cybersecurity training and development for the world’s largest companies,” he went on to say.
The National Science Foundation (NSF) is looking to help both the private sector companies as well as federal government agencies land highly trained experts who can fill the growing need for a highly skilled national cybersecurity workforce capable of responding to rapidly evolving challenges in the age of artificial intelligence .
As part of its CyberCorps Scholarship for Service (SFS) program, NSF is providing more than $29 million in scholarships over the next five years to eight universities. These new grantees join the current 82 universities that are part of the NSF CyberCorps Scholarship for Service program, representing 37 states, the District of Columbia and Puerto Rico.
The eight 2022 awardees include:
Oakland University
Fordham University
Indiana University – Purdue University Indianapolis
State University of New York at Binghamton
Georgia State University
University of Nevada, Reno
University of Memphis
Embry-Riddle Aeronautical University.
“As cyber threats continue to evolve in complexity, so must our approaches to cybersecurity education and our workforce,” NSF director Sethuraman Panchanathan said in a news release from Georgia State University. “The cybersecurity talent shortage remains a critical issue in the United States, with businesses and government agencies alike struggling to fill critical cybersecurity positions.
“These new CyberCorps Scholarship for Service projects engage diverse student populations and provide innovative and high-quality educational experiences that will ensure our nation is prepared to meet future cyberthreats with a well-trained workforce,” Panchanathan continued.
The NSF program is meant to increase the volume and strength of the nation’s cybersecurity workforce by providing full scholarships and stipends to students who agree to work in cybersecurity jobs for federal, state, local or tribal governments after graduation.
Over a five-year period, the project will provide scholarships to students studying issues at the intersection of cybersecurity and AI.
The universities said that SFS students will be prepared with the knowledge and practical skills to apply:
— AI expertise to cybersecurity and privacy problems
— Understand AI’s safety, security, privacy, reliability, fairness and ethical implications
— Build robust and trustworthy AI systems
“Our students will be capable of responding to rapidly evolving cybersecurity challenges in the age of AI,” said Daniel Takabi, associate professor of computer science at Georgia State University.
Balasubramaniam Ramesh, distinguished university professor and chair of the Department of Computer Information Systems at Georgia State added: “We are excited by the opportunity to prepare minority, women and veteran students for NSF’s CyberCorps.”
Federal officials went on to mention that SFS students will participate in an intensive academic program in cybersecurity, privacy and trustworthy AI, including coursework and research in cutting-edge areas to sharpen their creative thinking.
In addition, the SFS scholars will engage in experiential learning through opportunities for individual and group research projects and other extracurricular activities, which will provide deeply technical as well as interdisciplinary learning experiences and leadership development tailored to each student’s preparation and aspirations.
“Cybersecurity is arguably one of the most important challenges confronting society in the information age. Neither governments nor individuals are exempt from the ravages of cyber attacks. However, posing cyber conflict solely in terms of classic attackers and defenders understates the diversity and subtlety of the motivations, incentives, ethics, asymmetries and strategies of the constituent actors in cyberspace,” the NSF said.
“The intelligent adversary, whether a nation-state actor, an activist group, or a criminal, learns and evolves to exploit, disrupt, and overpower. Addressing the challenge of cybersecurity requires a coordinated multi-disciplinary approach, contributing to the body of knowledge on cybersecurity in multiple disciplines and leading to practical, deployable technologies,” the agency continued.
“These efforts require an innovative and efficient cybersecurity education system that will create an unrivaled cybersecurity workforce critical to U.S. national security, continued economic growth and future technological innovation in secure cyberspace,” NSF went on to say.
The National Automobile Dealers Association is looking to help members keep their information secure at the dealership.
On Wednesday, NADA said Accelerate2Compliance (A2C) has been chosen as a vendor within the association’s Affinity Provider Program.
NADA noted that A2C offers what’s designed to be an easy-to-use information security compliance solution through the A2C Portal, a turnkey cloud-based subscription to achieve, manage, and help maintain information security regulatory compliance requirements with a full suite of necessary tools.
NADA mentioned that A2C also offers users a detailed dashboard identifying areas of potential risk and remedial solutions for the compliance deficiencies identified.
“NADA members are focused more than ever on protecting their business and ensuring that they are compliant with data security regulatory requirements,” NADA president and chief executive officer Mike Stanton said in a news release. “The A2C portal is designed as a dealer friendly and easy to use cloud-based tool that allows our members to efficiently manage and stay on top of the ever-increasing security compliance requirements at both the federal and state levels.”
NADA recapped that its Affinity Provider program is tailored to provide members with access to discounted pricing for select vendor products and services that help dealers address the issues and opportunities that are critical to their businesses.
While NADA serves as the clearinghouse, the association said Affinity providers offer products and services that are responsive to dealer demands, and providers are carefully selected once NADA has examined a number of vendor products and services.
The service provider acknowledged that dealers are consistently challenged with achieving privacy and data-security regulatory compliance requirements as they guard against ever-increasing information security threats. A2C’s all-in-one cloud-based software solution is designed for dealers and their vendors to efficiently and cost-effectively build and manage their required information security program.
“We know the last thing our auto dealer clients want to see is a data breach that could harm them financially and reputationally, which is why they are constantly working to keep their information security programs compliant,” A2C chief executive officer Greg Pfleider said in the news release.
“Staying on top of privacy and data security regulatory requirements, including significantly expanded requirements found in the final amendments to the FTC’s Safeguard Rule, only complicate this task, which is why we built our A2C Portal that makes managing these expanded requirements simple and easy,” Pfleider went on to say.
For more information on A2C, go to this website. For more information about the NADA Affinity Provider Program, go to this website.
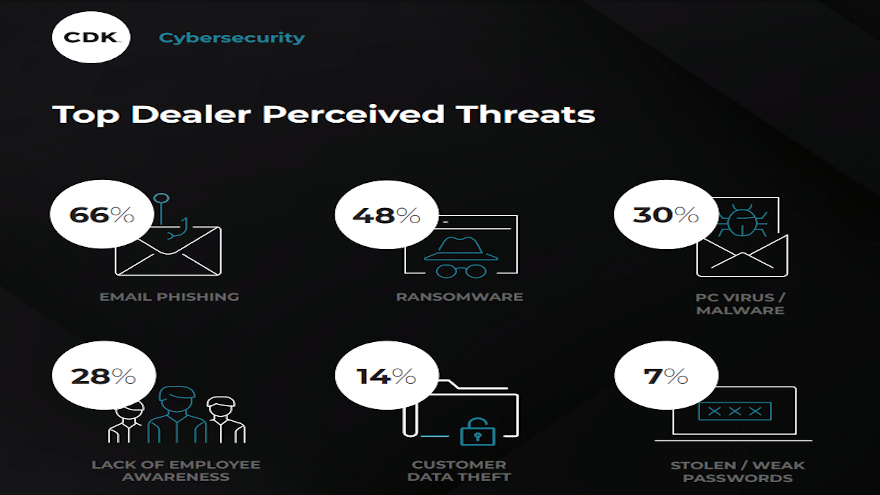
Especially in the advent of digital retailing, CDK Global sought to gauge how much dealerships are looking to protect themselves and their customers from online threats.
According to findings from a CDK Global study released on Wednesday, rising concerns of ransomware and phishing attacks impacting have prompted nearly half of dealers surveyed to plan for increased investments in cybersecurity in 2022. That’s compared to only 24% of dealers that invested in security measures in 2020.
“Meeting consumer demand for online automotive retailing while operating on an outdated framework can create a perfect storm for a cybersecurity breach,” said Joe Bell, vice president of IT solutions and global network architecture at CDK Global.
“By adding protective layers of security through integrated visibility and monitoring tools, dealerships can mitigate their risk of lengthy downtime for data recovery,” Bell continued in a news release.
CDK Global pointed out that IT-related business interruptions can be costly errors for dealerships, impacting businesses an average of 16 days in lost revenue if targeted by a cyberattack. Company expects said that recovering from a data breach and restoring a dealer’s reputation is both costly and time intensive, and automotive retailers may fall prone to meeting cybercriminals’ demands to keep their dealerships running.
In fact, recent data by ransomware specialty company Coveware shared in the CDK Global news release showed that payouts by businesses nearly quadrupled from 2019 to 2020, jumping from nearly $44,000 to $169,000.
CDK added that its cybersecurity report highlighted the need for dealerships to put necessary preventative measures in place to stem future incidents, including:
— While dealerships recognize there is an increased sense of urgency to prioritize cybersecurity relative to other operational areas (85%), only 49% believe they currently have adequate protection against cyberattacks.
— Employee email phishing remains the biggest perceived threat to dealer businesses (66%), but less than a third of employees have received formal security training on how to avoid it. Additional concerns include ransomware (48%) and malware (30%).
— A total of 65% of dealerships are regularly backing up data, system images and configurations and keeping the backups offline, but 73% are not testing their cyberattack incident response plan.
“Investing in modernizing aging security products, educating employees on increasingly sophisticated and frequent threats, and solidifying disaster recovery plans before an incident occurs can uphold a dealership’s reputation in the marketplace,” Bell said.
“If an automotive retailer’s cybersecurity plan for prevention, protection and response is firmly in place, dealerships can focus on strengthening the consumer buying experience while building trust,” he continued.
The company recapped that the CDK Global inaugural Dealership Cybersecurity Report was conducted in June among a national sample of 135 dealerships. The interviews were conducted online by CDK Research & Insights.
Participants included dealer executives, IT decision makers and departmental influencers within the dealerships.
To view CDK’s Dealership Cybersecurity Report, go to this website.
Industry collaboration is continuing to strengthen to combat online malfeasance.
The Financial Services Information Sharing and Analysis Center (FS-ISAC) — a global cyber intelligence sharing community solely focused on financial services — recently announced that global cyber intelligence sharing among its member financial firms increased by 60% in the period from August 2020 to August 2021.
The organization said two areas drove the rise in intelligence sharing: supply chain and ransomware threats. FS-ISAC indicated large scale threats resulted in record-breaking peaks of intelligence sharing across all regions: North America; Latin America; Europe, UK, Middle East and Africa; and Asia Pacific.
To increase global collaboration and encourage cybersecurity talent development, FS-ISAC launched its Global Leaders awards. This year, cybersecurity professionals from American Express, Banco Falabella Chile, Australia’s IAG, and UBS were recognized with the award for outstanding cyber intelligence sharing efforts.
“With the increase in sophisticated cross-border cyber criminal campaigns against the financial sector and its supply chain, sector-wide global collaboration has become a risk management imperative,” FS-ISAC chief executive officer Steven Silberstein said in a news release.
In addition to helping detect and prevent cyberattacks, FS-ISAC pointed out that sharing by larger financial institutions based in markets with stricter and more comprehensive regulation helps strengthen the cybersecurity programs of smaller or less resourced firms around the world, benefitting the full financial ecosystem.
“Intelligence and best practice sharing across our community and platforms has reached new heights, spurred by the high-profile events of the last 12 months. We commend the members who go above and beyond to protect the financial system at large,” Silberstein continued.
Member nominations for the accolades took place from the last week of March until June 30. Nominations were vetted by FS-ISAC’s Global Intelligence Office for impact and quality of contributions and narrowed down to three finalists per region.
The FS-ISAC board of directors, composed of chief information security officers at leading financial firms around the world, voted on one winner from each region.
Executives from each of the award-winning firms shared their reactions.
Fred Gibbins is chief information security officer at American Express.
“American Express is deeply interconnected with the other players in the global financial system,” Gibbins said. “We believe it is our critical responsibility to share intelligence and best practices with our peers to help the industry to protect and defend against emerging cyber threats. We are honored to be recognized by FS-ISAC and appreciate the collaboration between all the members for our collective protection.”
Juan Carrasco is head of cybersecurity at Banco Falabella Chile.
“In Latin America we benefit from intelligence that is shared by global US and Europe-based firms as well as from our neighboring countries,” Carrasco said. “By monitoring attacks in Argentina and Brazil, we were able to predict and thwart a cyber attack in Chile. This attests to the power of cross-border intelligence sharing in mitigating cyber risk.”
Craig Hall is threat analytic cell manager at IAG.
“Meaningful threat intelligence gives our security team at IAG an advantage over the attackers and reduces cyber risk,” Hall said. “Recently, we were able to identify a threat actor who methodically attacked Australian financial institutions in alphabetical order throughout the day. By sharing the criminal’s tactics, members throughout the region knew when they were likely to get hit and were therefore able to defend against attacks.”
Corsin Camichel is cyber threat intelligence regional lead at UBS.
“As a global firm, UBS monitors the global cybersecurity landscape to proactively detect and mitigate risks,” Camichel said “Sharing intelligence and best practices with our peers and regional counterparts is fundamental to staying ahead of emerging cyber threats. I am honored by this award and will continue to share with my colleagues and peers around the world.”
Cybersecurity Awareness Month started on Friday.
It’s an initiative now in its 18th year led by the National Cyber Security Alliance (NCSA), in partnership with the Cybersecurity and Infrastructure Security Agency (CISA), to ensure that everyone has the resources they need to be safer and more secure online.
Officials highlighted that this year’s theme for the month-long campaign is “Do Your Part. #BeCyberSmart.” According to a news release this theme encourages individuals and organizations to own their role in cybersecurity, stressing personal accountability and the importance of taking proactive steps to enhance security in our increasingly connected world.
NCSA interim executive director Lisa Plaggemier explained that the line between our online and offline lives is indistinguishable, and our homes, societal well-being, economic prosperity and nation’s security are impacted by the security of our technology.
Plaggemier said that if individuals and organizations do their part in implementing stronger security practices, raising community awareness, educating vulnerable audiences, or training employees that our interconnected world will be safer and more resilient for everyone.
“We’ve seen an unprecedented shift to more digital usage in the last year and there’s no going back,” Plaggemier said in the news release. “The onset of the ongoing pandemic and the need to stay connected has made our digital life prone to cyber threats now more than ever. As such, it’s critical that we adopt cyber safe practices that can keep our devices and access to our personal data safe and reduce the risk of exposure.”
Throughout October, NCSA will focus on the following areas in promotions and outreach:
Week 1: Be Cyber Smart.
Week 2: Fight the Phish!
Week 3: Explore. Experience. Share. – Cybersecurity Career Awareness Week
Week 4: Cybersecurity First
During Cybersecurity Awareness Month, NCSA, CISA and key partners also will share resources and engage on social media to drive increased visibility around the month’s key messages and themes to keep consumers and organizations informed about cybersecurity best practices.
CISA has provided additional Cybersecurity Awareness Month resources that can be shared with stakeholders and used in your communities throughout the year to encourage strong, nationwide cybersecurity. Those resources can be found at https://www.cisa.gov/national-cybersecurity-awareness-month-resources.
By signing up to become a Cybersecurity Awareness Month Champion, NCSA highlighted organizations and individuals can become a part of October’s campaign to help promote a safer, more secure, and more trusted connected world.
Upon registration, all champions receive a toolkit of material to help them implement cybersecurity awareness initiatives and activities during Cybersecurity Awareness Month.
To learn more and sign up, visit https://staysafeonline.org/cybersecurity-awareness-month/champions/.
Plaggemier — who has an affinity for the automotive industry since her professional career includes time at Ford and CDK Global — previously discussed how dealerships and finance companies can remain secure during an episode of the Auto Remarketing Podast available below.